Customers of Sisense data analytics service urged to change credentials

The US Cybersecurity and Infrastructure Security Agency (CISA) is urging organizations to change any credentials they might have shared or stored with Sisense, a data analytics software and services provider, due to a compromise that’s still being investigated.
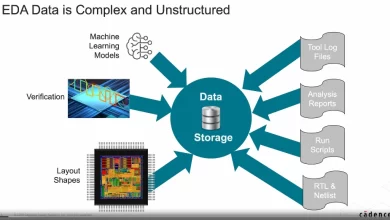
Sisense’s platform allows companies to connect various data sources including databases, spreadsheets, cloud services and web applications and then use the platform’s tools to analyze that data and generate reports and visualizations. The company’s customers include major companies from various industries including healthcare, retail, manufacturing, technology, financial services and pharma.
“CISA is taking an active role in collaborating with private industry partners to respond to this incident, especially as it relates to impacted critical infrastructure sector organizations,” the agency said in an alert.
Sisense did not immediately respond to a CSO request for comment, but independent journalist Brian Krebs published a copy of the message that Sisense CISO Sangram Dash sent to the company’s customers. In the message Dash warns that “certain Sisense company information may have been made available on what we have been advised is a restricted access server (not generally available on the internet).”
It’s not clear if this refers to a Sisense server that was inadvertently exposed to external access or to a server where the information was stored by attackers after being stolen as a result of a security breach of the company’s systems. According to CISA, the incident was discovered by independent security researchers and involved Sisense customer data.
Dash advised customers to promptly rotate any credentials they use in their Sisense application, a recommendation that was echoed by CISA. The agency also told users to investigate any potentially suspicious activity involving credentials they shared with the company.
The Sisense platform has multiple deployment options, including a cloud version managed by Sisense, a version that can be deployed on the customer’s own cloud and one that can be deployed on premise. The platform offers many plug-ins and integration options, as well as a software development kit (SDK) that developers can integrate into their own applications.
“The nature of Sisense is they require access to their customers’ confidential data sources,” security researcher Marc Rogers said on X. “They have direct access to JDBC connections, to SSH, and to SaaS platforms like Salesforce and many more. It also means they have tokens, credentials, certificates often upscoped. The data stolen from Sisense contained all these tokens, credentials and access configurations.”
“This is a worst-case scenario for many Sisense customers,” Rogers noted. “These are often literally the keys to their kingdoms. Treat it as an EXTREMELY serious event.”
Meanwhile, security researcher Dave Kennedy advised Sisense customers to change any API keys in addition to passwords to Sisense accounts and to look for any unusual activity dating from April 5th onward.