Cybersecurity
-

AI, cybersecurity investments and identity take center stage at RSA 2024
Worries about AI-based attacks are also driving increased security adoption in organizations. In one presentation, an Akamai senior vice president…
Read More » -

Zighra behavioral biometrics contracted for Canadian government cybersecurity testing
Zighra has won a contract with Shared Services Canada (SSC) to protect digital identities with threat detection and Zero Trust…
Read More » -

Securing our digital frontlines – The Jerusalem Post
Imagine waking up to find that Israel’s power grid has been hacked, plunging the nation into darkness. Hospitals scramble…
Read More » -
Cybersecurity With Human-AI Collaboration – USC Viterbi
ILLUSTRATION BY DEM10/ISTOCK As organizations increasingly rely on networks, online platforms, data and technology, the risks associated with data breaches…
Read More » -

EU cybersecurity chief says disruptive attacks have doubled in the EU in 2024 |
Disruptive digital attacks – many traced to Russia-backed groups – have doubled in the European Union in 2024 and are…
Read More » -

New research reveals impact of AI and cybersecurity on women, peace and security in south-east Asia
Credit: Pixabay/CC0 Public Domain Systemic issues can put women’s security at risk when artificial intelligence (AI) is adopted, and gender…
Read More » -

Study: MSPs Struggle to Keep Up With Cybersecurity Challenges
Many managed service providers (MSPs) are struggling to keep up with changes in cybersecurity, according to a recent study by…
Read More » -
New TEDCO Study Outlines Steps for Developing Maryland’s Cybersecurity Workforce
Findings include a misalignment of cybersecurity workforce supply and demand COLUMBIA, Md., May 29, 2024 /PRNewswire/ — TEDCO, Maryland’s economic engine for…
Read More » -

FBI’s Pittsburgh office has new special agent in charge: a cybersecurity expert
MENU ACCOUNT SECTIONS OTHER CLASSIFIEDS CONTACT US / FAQ Source
Read More » -
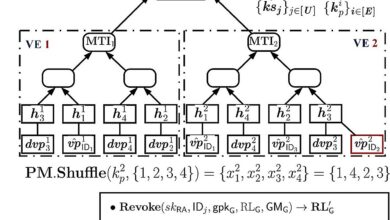
Enhancing cybersecurity with ‘moving trees’
High-level Merkle Tree Structure. Credit: IEEE Transactions on Information Forensics and Security (2024). DOI: 10.1109/TIFS.2024.3386350 “Please enter the code within…
Read More »