U.S. Dismantles World’s Largest 911 S5 Botnet with 19 Million Infected Devices

The U.S. Department of Justice (DoJ) on Wednesday said it dismantled what it described as “likely the world’s largest botnet ever,” which consisted of an army of 19 million infected devices that was leased to other threat actors to commit a wide array of offenses.
The botnet, which has a global footprint spanning more than 190 countries, functioned as a residential proxy service known as 911 S5. A 35-year-old Chinese national, YunHe Wang, was arrested in Singapore on May 24, 2024, for creating and acting as the primary administrator of the illegal platform from 2014 to July 2022.
Wang has been charged with conspiracy to commit computer fraud, substantive computer fraud, conspiracy to commit wire fraud, and conspiracy to commit money laundering. If convicted on all counts, Wang faces a maximum penalty of 65 years in prison.
The Justice Department said the botnet was used to carry out cyber attacks, financial fraud, identity theft, child exploitation, harassment, bomb threats, and export violations.
It’s worth noting that Wang was identified as the proprietor of 911 S5 by security journalist Brian Krebs in July 2022, following which the service abruptly shut down on July 28, 2022, citing a data breach of its key components.
Although it was resurrected under a different brand name called CloudRouter a few months later, according to Spur, the service has since ceased operations sometime this past weekend, the cybersecurity company’s co-founder Riley Kilmer told Krebs.
“Wang and others are alleged to have created and disseminated malware to compromise and amass a network of millions of residential Windows computers worldwide,” according to an unsealed indictment.
“These devices were associated with more than 19 million unique IP addresses, including 613,841 IP addresses located in the United States. Wang then generated millions of dollars by offering cybercriminals access to these infected IP addresses for a fee.”
Residential proxies (RESIPs) are networks of legitimate user devices that route traffic on behalf of paid subscribers. It typically involves the providers renting access to redirect network traffic through computers, smartphones, or routers belonging to real users.
The main objective of using such proxyware services to funnel traffic through the IP addresses of these devices so as to anonymize the source of the malicious requests.
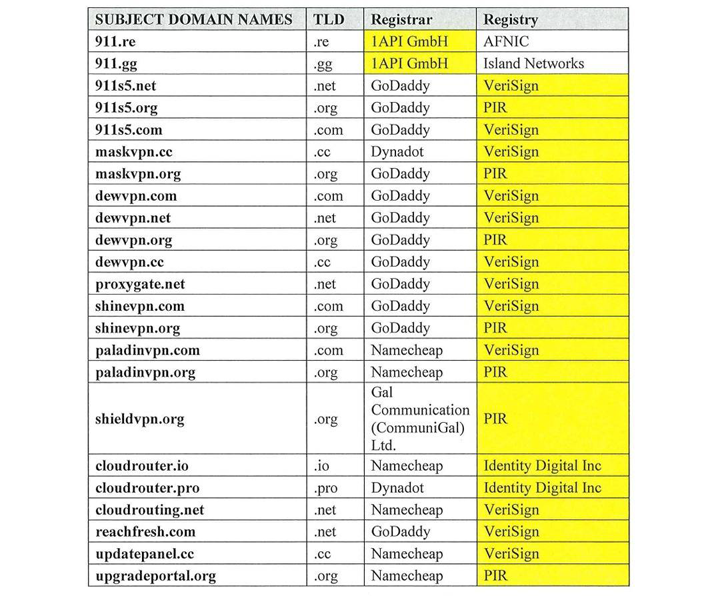
Court documents accuse Wang of allegedly propagating the malware through free Virtual Private Network (VPN) programs, such as MaskVPN and DewVPN, as well as other pay-per-install services that bundled it with pirated software.
The defendant is estimated to have managed an infrastructure encompassing 150 servers worldwide, 76 of which were taken from U.S. based online service providers.
“Using the dedicated servers, Wang deployed and managed applications, commanded and controlled the infected devices, operated his 911 S5 service, and provided paying customers with access to proxied IP addresses associated with the infected devices,” the DoJ said.
It’s also alleged that 911 S5 allowed criminal actors to bypass financial fraud detection systems and steal billions of dollars from financial institutions, credit card issuers, and federal lending programs, including pandemic relief and the Economic Injury Disaster Loan (EIDL) program, by submitting fraudulent claims that originated from compromised IP addresses.
Furthermore, the service made it possible for attackers residing outside the U.S. to purchase goods with stolen credit cards or criminally derived proceeds, and illegally export them outside of the country in contravention of U.S. export laws.
Wang, for his part, is estimated to have received approximately $99 million from selling access to the hijacked proxied IP addresses, using the ill-gotten money to purchase four luxury cars, several expensive wristwatches, and 21 residential or investment properties across the U.S., China, Singapore, Thailand, and the U.A.E.
Other digital assets owned by Wang include over a dozen domestic and international bank accounts and more than 24 cryptocurrency wallets, which were used to pull off the scheme. Blockchain analytics firm Chainalysis revealed that the addresses associated with Wang hold $136.4 million in cryptocurrency.
The takedown, a result of a coordinated effort between U.S., Singapore, Thailand, and Germany, has resulted in the disruption of 23 domains and over 70 servers that constitute the crux of 911 S5. The effort also saw the seizure of assets valued at approximately $30 million.
Concurrent with Wang’s indictment, the Department of the Treasury’s Office of Foreign Assets Control (OFAC) levied sanctions against the defendant along with his co-conspirator Jingping Liu and power of attorney Yanni Zheng for their activities associated with the 911 S5 botnet and the residential proxy service.
The agency also sanctioned three Thailand-based entities, namely Spicy Code Company Limited, Tulip Biz Pattaya Group Company Limited, and Lily Suites Company Limited, that are said to be owned or controlled by Wang, noting that Spicy Code Company Limited was used to buy real estate properties in the country.
“The conduct alleged here reads like it’s ripped from a screenplay: A scheme to sell access to millions of malware-infected computers worldwide, enabling criminals over the world to steal billions of dollars, transmit bomb threats, and exchange child exploitation materials,” said Matthew S. Axelrod of the U.S. Department of Commerce’s Bureau of Industry and Security (BIS).
“What they don’t show in the movies though is the painstaking work it takes by domestic and international law enforcement, working closely with industry partners, to take down such a brazen scheme and make an arrest like this happen.”